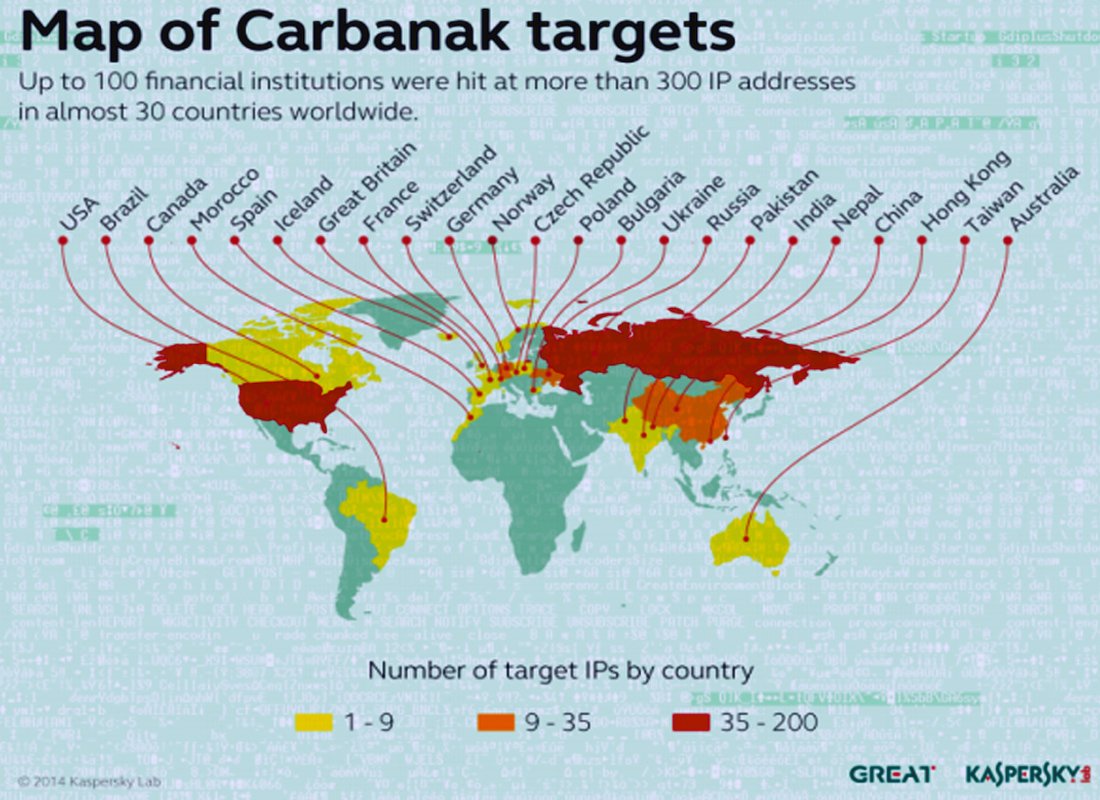
So is it Caranak or Anunak? Well basically Annuak is the name of the malware given by the authors themselves. While Carbanak is the name the antivirus industry gave this malware. So basically they are one and the same with regards to reporting.
So this cybercriminal gang is very sophisticated in fact they are one of a few APT-like criminal groups currently being tracked by Kaspersky Labs and Fox-IT. If you remember this gang breached Staples last year and stole 1.16 million payment cards.
The report from Kaspersky suggests that the gang deployed the malware via phishing scams directed at more than 100 banks, online payment systems and other financial institutions in about 30 countries. Its estimate that they stole between $300 million to $1 billion dollars.
Phishing scams continue to be effective as the weakest link in any security program continues to be people. As one can see from this attack, even banks with notoriously well secured environments are not immune to these types of threats. Less sophisticated organizations are even more at risk.
Other threats exist such as the Dyre banking Trojan, which undertook a sudden and rapid evolution of their malware and infrastructure in late 2014. The gang responsible has also modified their TTP in an attempt improve delivery and installation rates. As Proofpoint concluded “The sudden and rapid evolution of Dyre to incorporate evasion techniques often associated with more sophisticated, targeted threats highlights a central challenge of today’s threat landscape: an increasingly broad spectrum of malware and attacks are leveraging the techniques that have made advanced threats so effective at bypassing traditional signature- and reputation-based defenses. Not only does email remain the primary threat vector for organizations, but the evolution of Dyre demonstrates that organizations can no longer distinguish between high-volume nuisances like spam and low-volume, targeted threats, but must instead adapt to face a landscape in which all unsolicited email must be treated as a potential threat, and at that one which will employ advanced threat techniques.”