Logic Bounce was founded in 2013 with the mission of empowering businesses and helping communities around the world to embrace digital transformation securely. We built our company, technology and culture with a singular focus on protecting our clients by delivering high quality research-driven cybersecurity solutions.
A Trusted Advisor
We are the trusted advisor to our clients who enjoy the following tangible benefits from the partnership:
- Client Focused: A deep comprehensive understanding of our clients strategic and business needs. This approach allows us to deliver security solutions that fuel innovation and growth, not restrict them.
- Powered by Research: Research powers everything we do. Every consultant devotes 25% of their time to security research. This investment ensures that not only are our consultants at the bleeding edge of security but they can leverage this knowledge to provide clients a unique perspective on the threats they face.
- Continuous Improvement: Quality of execution is inherent in everything we do. We measure, monitor, analyse and improve productivity, processes and ourselves to satisfy our clients and do better than yesterday. We work with enthusiasm and intellect and are driven to surpass what has already been achieved.
- Unbiased Technical Expertise: We have the skills and experience to defend against the most advanced threats that businesses face. We hate hype, abhor buzzwords and emphasis the outcomes a client receives. At the end of the day we only answer to our clients.
- Global Reach: With offices in Asia, Europe and North America we can service clients on a truly global basis. This global reach enables us to take advantage of talent across the globe. Our clients can trust they are working with the best in the industry.
Innovate Your Cybersecurity to Innovate Your Business
We believe that inadequate cybersecurity capabilities within companies is a silent disease that impedes and stifles business innovation. Its important for companies to understand that the digital economy is not just a digitised version of the current economy. Digital transformation, requires a strong cybersecurity foundation. With this foundation in place, companies will have the confidence to implement digital processes and technologies that fuel innovation and growth. Companies that turn cybersecurity excellence into competitive advantage can innovate faster and more fully purse the sorts of digital transformation that allows them to respond nimbly to rapidly changing markets. This agility makes them more effective and drives enhanced financial performance. Companies with subpar cybersecurity are in the worst possible competitive position: not innovating fast enough to compete, yet not fully protected from cybersecurity attacks despite delaying digital innovations. Building cybersecurity excellence is a significant driver of the success of digital products, services and business models and is overall driver of business value.
Cybersecurity excellence, also gives companies the opportunity to differentiate their brands by conveying a strong perception of customer trust. When prospects and customers trust that security and privacy breaches will not occur, that trust becomes an important brand attribute like quality, cost and customer experience. Companies can then achieve competitive advantage by promoting this capability to prospects and customers. From our perspective enhancing cybersecurity capabilities across an organisation is a win now and into the future for any organisation
The Threat Defence Platform
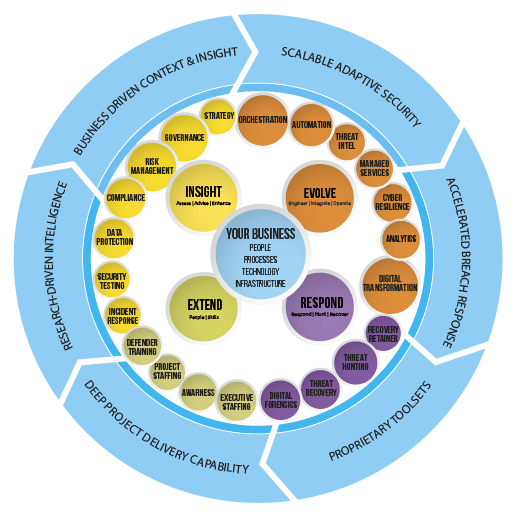
Our intelligence-driven Threat Defence Platform (TDP)enables organisations to fortify their cyber defences to prevent security breaches, detect malicious activity, prioritize and respond rapidly to security breaches and predict emerging threats. Our solutions leverage proprietary technologies, processes and extensive expertise in the information security industry. We address the full spectrum of security:
Strategy and Risk– Review and evaluate existing security programs, provide guidance and best practice on the development of a cybersecurity strategy and to understand the threats to critical assets, determining the level of risk these assets are exposed to and recommending the appropriate level of protection.
Controls & Compliance– Assess and guide remediation of compliance gaps and assure that your organisation is focusing on relevance of controls, time and budget in areas that add the most value or reduce risk.
Data Protection & Privacy– We assist your organisation with the development of a privacy and data protection program for a product line, branch or an entire organisation.
Offensive Security Testing & Assurance– Bespoke tactical assessments that deliver measurable improvements to security. For organisations with mature, well-implemented security programs, measure your capability to protect, detect and respond to an attack with an adversarial-based simulation against people, software, hardware and facilities.
Security Architecture and Operations– Innovate your security so you can innovate your business. Identify internal and external security risks and implement orchestration tools and data processing technologies to enhance your visibility, detection and response capabilities.
Cyber Resilience– The overriding goal is to help an organisation resume critical operations within an acceptable time frame following an interruption. Review your existing business continuity program across executive sponsorship, strategy & vision, organisation, processes, procedures, maintenance programs, applications, data, infrastructure and facilities.
Managed Security– Designed to serve as an extension of your security team. We help eliminate blind spots and provide visibility to what really matters. Continuously validate the security posture of your organisation. Gain usable intelligence about your environment so that you can address weaknesses in your security.
Threat Response, Hunt and Recovery– Guarantee fast response and availability of our elite Incident Recovery and Investigation team to contain, mitigate and help you recover from a security breach
Strategic and Project Staffing– Specialised project or executive level support to augment your team.
Education and Training– Address both the technical and human elements of your organisation to ensure you’re operating in a secure environment
Our flexible deployment model allows us to support the evolving needs of even the largest, most sophisticated enterprises staffed with in-house security experts, as well as small and medium-sized businesses and government agencies with limited in-house capabilities and resources. Our vendor-neutral approach enables our clients to enhance their evolving IT security infrastructure, appliances and “best of breed” technologies with our solutions and capabilities, which provide our clients with both a comprehensive and highly effective security defence posture.
If you have any questions or have security challenges we would love to share our thoughts and experiences and see if we can help. Contact us here